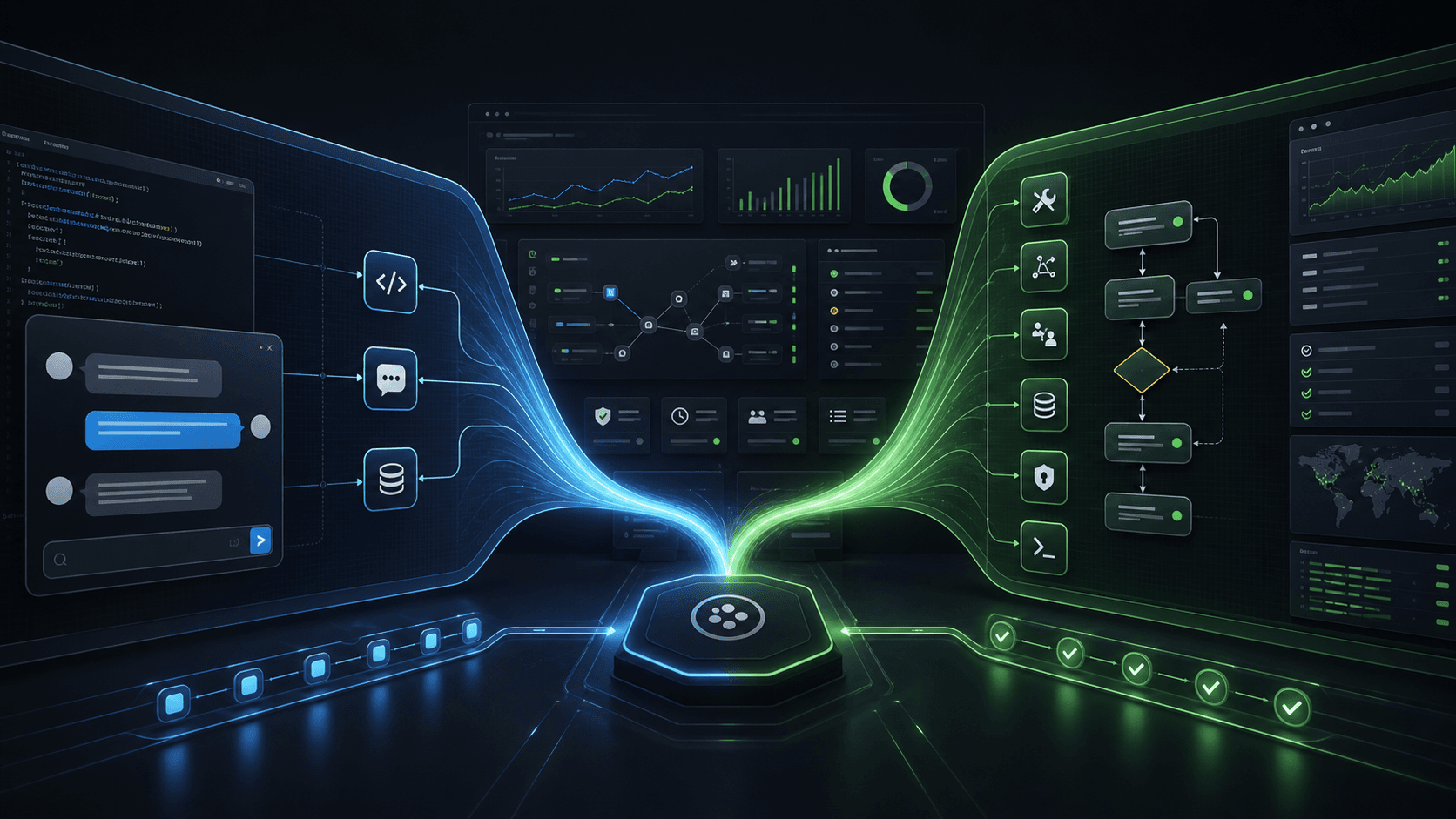
Running an agent against a real repository is where it gets useful — and where small security mistakes turn into big problems.
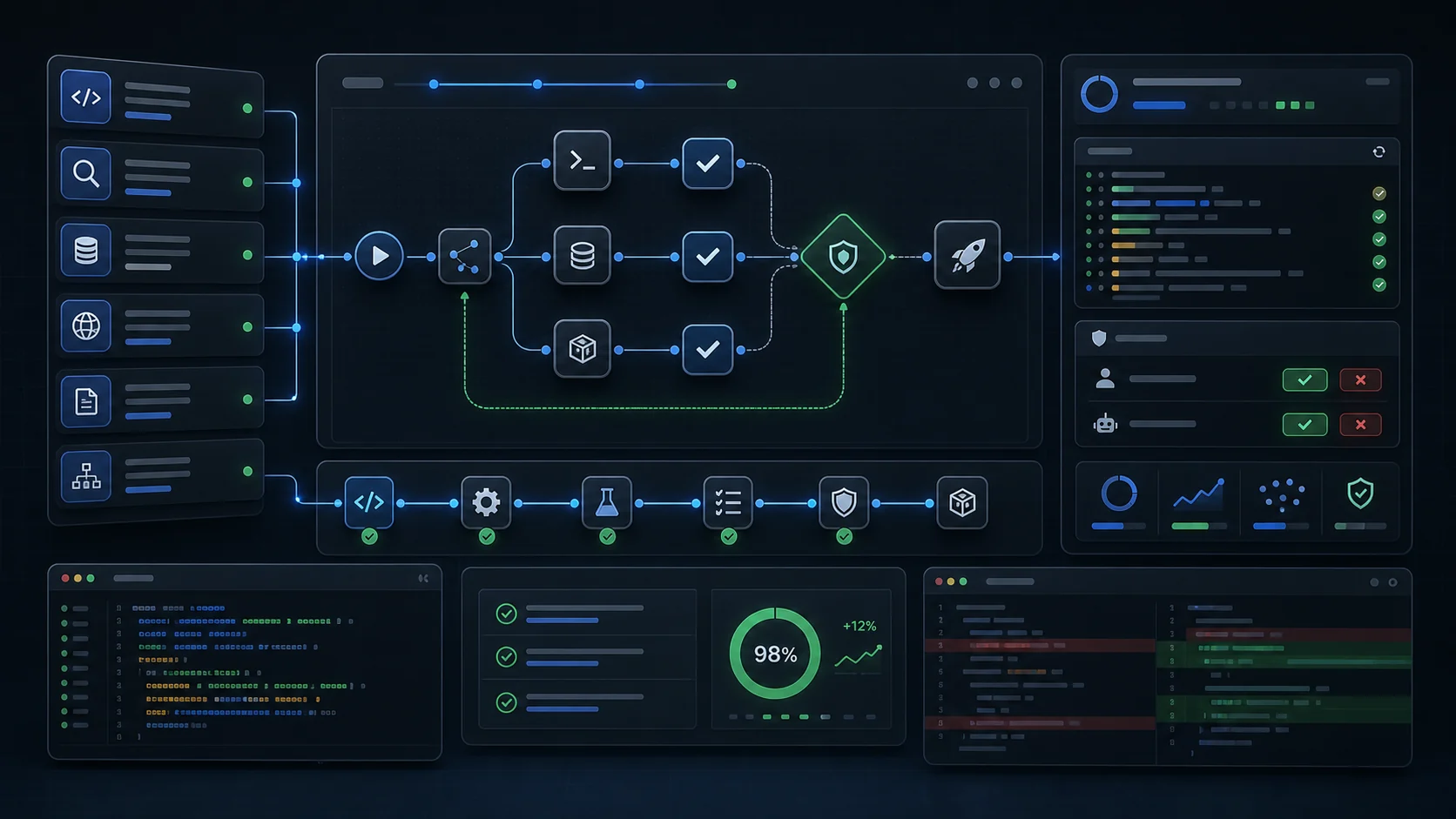
This post is the playbook we use to run an OpenClaw bot reliably:
- skills that route correctly
- long-running tasks that don’t fall apart
- secure GitHub access without leaking credentials
If you’re building AI workflows for growth + operations, start here: https://zeiko.io.
1) Skills are routing logic (not marketing)
A skill’s description is the model’s decision boundary. Write it like a filter:
- Use when: concrete triggers (inputs, file types, tools used)
- Do NOT use when: negative examples (common misroutes)
- Output: what the skill should produce
Example:
- “Use when the user pasted a WhatsApp chat and wants a reply. Do NOT use for reminders or gateway troubleshooting.”
Why it matters: when you add multiple skills, routing gets harder unless each skill has a sharp edge.
2) Add negative examples and edge cases
This is the fastest way to improve accuracy.
Add 3–6 bullets like:
- “Don’t call this skill when the user is asking for X. Use <other-skill> instead.”
- “If the time is ambiguous (9am vs 9pm), ask one question instead of guessing.”
3) Put templates inside skills
Templates inside skills are effectively free until invoked.
Examples:
- WhatsApp reply templates (reschedule, confirmation, apology, boundary)
- Research brief template (summary, key points, risks, sources)
- Diagnostic checklist (what to capture before restarting services)
4) Determinism lever: explicitly call the skill
When you want reliability over creativity, don’t rely on routing:
“Use the <skill-name> skill.”
This turns “maybe” into a contract.
5) Long-run durability: artifacts + commits
Agents work best when there’s a clean handoff boundary.
Artifacts
Write real outputs to disk:
- plans, briefs, reports
- exports (CSV/PDF)
Commits
Keep changes reviewable:
- small commits
- clear messages
- prefer PRs for user-facing changes
If you’re building productized automation and want a repeatable workflow, Zeiko can help: https://zeiko.io.
6) Security posture: skills + networking is high risk
Combining a powerful procedure (skills) with open network access creates an easy exfiltration path.
Defaults that keep you safe:
- Never embed tokens in URLs (git remotes, webhooks, logs)
- Least privilege tokens/keys
- Confirm before outbound actions (posting, messaging, irreversible ops)
7) Secure GitHub access for an OpenClaw bot
“GitHub access” usually means two different things:
- Git transport (clone/push)
- Best for single-repo scope: SSH deploy key
- Alternative: HTTPS + credential helper (avoid token-in-URL)
- GitHub API (list PRs, comment, labels)
- Use GitHub CLI (
gh) with a fine-grained token
Don’t do:
- ❌
https://TOKEN@github.com/OWNER/REPO.git
It leaks in logs, shell history, and screenshots.
Revocation (instant kill switch)
If anything feels off:
- revoke the token
- remove the deploy key
- rotate credentials
8) A “safe default” setup
For most teams:
- Deploy key (write) for git pushes
- Fine-grained PAT (repo-scoped) for PR operations
- Separate “bot” identity from human credentials
If you want to build secure, repeatable agent workflows (not just demos), start at https://zeiko.io.